table of contents
Data Privacy & Protection: A Security Auditor’s Essential Guide
Data is the lifeblood of the modern world, flowing through every aspect of our lives. From the moment we wake up to the time we go to sleep, we generate and interact with data. This makes data privacy and protection not just a technical concern, but a fundamental human right. In the vast landscape of information technology, security auditors stand as vigilant guardians, tasked with ensuring that this precious resource is handled responsibly and securely. This guide will provide a comprehensive overview of the security auditor’s role in data privacy and protection. We’ll explore the key areas of responsibility, from regulatory compliance to incident response, offering valuable insights for both seasoned professionals and those new to the field.
Understanding the Landscape of Data Privacy Regulations
The world of data privacy is a complex and ever-evolving one, with a multitude of regulations shaping how organizations collect, process, and store personal information. For a security auditor, a solid understanding of these regulations is not just beneficial; it’s absolutely essential. Without this understanding, it’s impossible to effectively assess an organization’s compliance posture. It’s also impossible to advise on how to protect data.
GDPR, CCPA, and Beyond: Key Regulations
The General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the United States are two of the most prominent data privacy regulations worldwide. GDPR sets a high standard for data protection, requiring organizations to obtain explicit consent for data collection, provide individuals with rights to access and control their data, and implement robust security measures to protect against data breaches. CCPA, on the other hand, grants California residents similar rights, including the right to know what personal information is collected, the right to delete it, and the right to opt-out of its sale. Moreover, other regulations, such as the Health Insurance Portability and Accountability Act (HIPAA) in the healthcare sector and the Personal Information Protection and Electronic Documents Act (PIPEDA) in Canada, add further layers of complexity.
The Importance of Staying Updated
Data privacy regulations are not static. They are dynamic, constantly changing to reflect the evolving landscape of technology and societal expectations. New laws are enacted, existing regulations are amended, and enforcement practices shift. Therefore, the security auditor must stay informed about these changes through continuous learning, attending industry conferences, and subscribing to relevant publications. Staying current on data privacy laws and regulations ensures that audits are comprehensive, accurate, and relevant. This will ultimately help organizations maintain compliance and mitigate risks.
Conducting Data Privacy Assessments: A Deep Dive
A core responsibility of a security auditor is conducting thorough data privacy assessments. These assessments involve a systematic evaluation of an organization’s data handling practices against relevant regulatory requirements and industry best practices. These assessments are crucial for identifying vulnerabilities, assessing risks, and recommending improvements to data privacy controls. Performing them correctly will determine the ultimate success or failure of the security auditor.
Scoping the Assessment: Defining the Boundaries
The first step in any data privacy assessment is to define the scope. This involves determining which data processing activities, systems, and departments will be included in the audit. It is important to set clear boundaries to ensure that the assessment is focused and efficient. The scope should align with the organization’s business objectives, regulatory obligations, and risk profile. Documenting the scope clearly is crucial for transparency and provides a reference point throughout the assessment process.
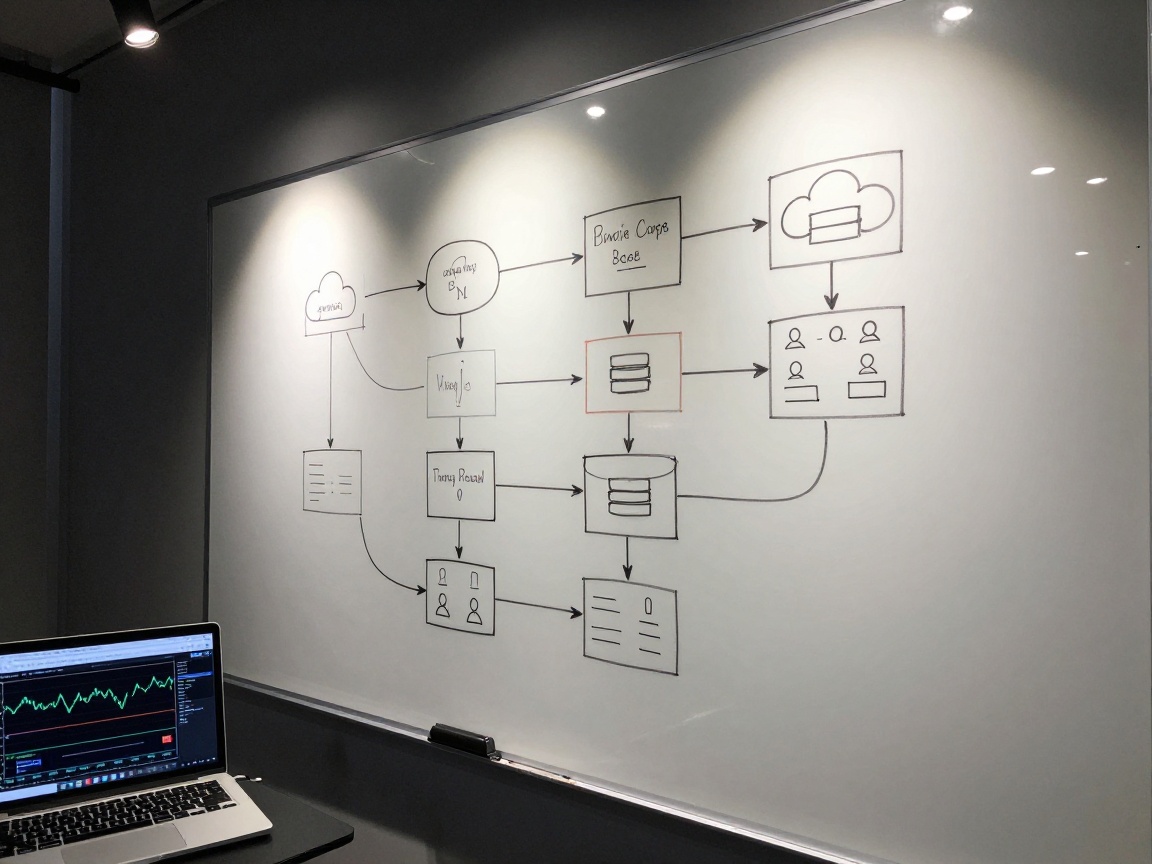
Data Mapping: Identifying Data Flows
Data mapping is a critical activity that involves identifying and documenting the flow of personal data within an organization. This includes determining where data originates, how it is processed, where it is stored, and with whom it is shared. Creating a data flow diagram is a useful technique, providing a visual representation of the data lifecycle. It helps the security auditor understand the organization’s data processing practices and identify potential vulnerabilities. The outcome of data mapping serves as a foundation for risk assessment.
Risk Assessment: Pinpointing Vulnerabilities
Once the data flows are mapped, the security auditor can perform a risk assessment. This involves identifying potential threats to data privacy, such as data breaches, unauthorized access, and data loss. Each threat is then assessed in terms of its likelihood and potential impact, resulting in a risk score. The risk assessment helps prioritize vulnerabilities, and determines which controls are most critical for protecting data. The auditor needs to know where the data might be vulnerable.
Developing and Reviewing Data Privacy Policies
Data privacy policies are the cornerstone of an organization’s data protection program. They provide a framework for how personal data should be handled, ensuring compliance with regulations and reflecting the organization’s commitment to data privacy. They serve as a roadmap for employees. Security auditors play a key role in developing, reviewing, and assessing the effectiveness of these policies. They are vital to ensuring that organizations meet all their obligations.
Key Components of a Robust Data Privacy Policy
A comprehensive data privacy policy typically includes several key components. It begins with a clear statement of the organization’s commitment to data privacy, and then it defines the types of personal data collected and how it is used. It must outline the rights of data subjects, such as the right to access, correct, and delete their data. It also describes how the organization protects data, including the security measures in place. The policy should also include a process for handling data breaches and a contact point for data privacy inquiries.
Policy Review: Ensuring Compliance and Effectiveness
A security auditor’s role in policy review involves evaluating the policy’s completeness, accuracy, and relevance. The auditor should assess the policy against applicable regulations and industry best practices. It’s critical to assess if the policy is effectively communicated to employees and data subjects. The auditor may recommend changes to improve the policy’s clarity, enforceability, and alignment with the organization’s data processing practices. A regularly reviewed policy will adapt to changing requirements and emerging threats.
Auditing Data Security Controls: The Technical Side
Data security controls are the technical and organizational measures implemented to protect data from unauthorized access, use, disclosure, disruption, modification, or destruction. Security auditors are essential for assessing the effectiveness of these controls, ensuring they are properly implemented, and aligned with the organization’s risk profile. They need to understand the intricacies of access control, encryption, and network security to conduct comprehensive audits.
Access Control and Authorization
Access control is a fundamental security control that governs who can access what data and resources. The security auditor should evaluate the organization’s access control mechanisms, including user authentication, authorization, and privilege management. The auditor should verify that access rights are based on the principle of least privilege, meaning employees only have the minimum level of access necessary to perform their jobs. They also should audit the access control logs for suspicious activity.
Data Encryption and Storage Security
Encryption is a critical measure for protecting data confidentiality, particularly during storage and transmission. The security auditor should assess the organization’s use of encryption, ensuring that it is properly implemented and managed. The auditor should also review the security of data storage systems, including servers, databases, and cloud storage. It’s vital to verify that data is stored securely, with appropriate access controls and monitoring in place.
Network Security and Monitoring
Network security involves protecting an organization’s network infrastructure from cyber threats. The security auditor should evaluate the effectiveness of network security controls, such as firewalls, intrusion detection systems, and security information and event management (SIEM) tools. They also should assess the organization’s network monitoring capabilities, ensuring that security events are detected, investigated, and responded to effectively. It’s vital to know where all the data comes from.
Evaluating Data Processing Agreements: A Critical Review
Organizations often rely on third-party vendors to process personal data. Data processing agreements are contracts that govern how vendors handle this data, and a security auditor’s role is to carefully evaluate these agreements to ensure that they meet regulatory requirements and protect data privacy. These agreements help the security auditor ensure the best protection of an organization’s data.
Key Clauses to Scrutinize
Data processing agreements should include key clauses that define the scope of processing, the types of data processed, and the purpose of processing. They should also specify the vendor’s obligations regarding data security, data breach notification, and data subject rights. The security auditor should carefully scrutinize these clauses to ensure that they are complete, accurate, and aligned with the organization’s data privacy policies and regulatory requirements.
Vendor Management and Due Diligence
Effective vendor management is a critical aspect of data privacy. The security auditor should evaluate the organization’s vendor selection and management processes, including due diligence procedures to assess the vendor’s data privacy and security practices. It should also verify that the vendor is compliant with data processing agreements and is providing adequate protection for personal data. Conducting proper vendor management is critical to making sure the organization is protected.
Monitoring Data Privacy Compliance: Ongoing Vigilance
Data privacy compliance is not a one-time effort; it’s an ongoing process. Organizations must continuously monitor their data handling practices, assess their compliance posture, and take corrective actions as needed. The security auditor plays a key role in establishing and maintaining a robust monitoring program. This process helps determine if all the appropriate measures are being taken to protect data.
Implementing Monitoring Tools and Processes
Effective monitoring requires the use of appropriate tools and processes. The security auditor should evaluate the organization’s monitoring tools, such as data loss prevention (DLP) systems, security information and event management (SIEM) tools, and data privacy monitoring platforms. They also should help establish monitoring processes, including regular reviews of security logs, data access logs, and audit trails. The right tools and processes can identify potential violations of data privacy requirements.
Regular Reporting and Analysis
Regular reporting and analysis are essential for providing insights into the organization’s data privacy compliance posture. The security auditor should assist in developing and implementing reporting mechanisms, including dashboards, metrics, and key performance indicators (KPIs). They also should help analyze the data collected, identify trends, and make recommendations for improvement. Proper reporting and analysis allow organizations to make data-driven decisions and maintain a strong compliance posture.
Training and Awareness Programs: Empowering the Workforce
Data privacy is a shared responsibility, and all employees have a role to play in protecting personal data. Training and awareness programs are essential for educating employees about data privacy principles, policies, and procedures. The security auditor is instrumental in designing, delivering, and evaluating these programs. Through these programs, the workforce becomes an active participant in protecting data.
Designing Effective Training Modules
Effective training modules should be tailored to the specific needs of the organization and its employees. The security auditor should help design training content that is engaging, relevant, and easy to understand. The training should cover key data privacy concepts, such as data subject rights, data security best practices, and incident response procedures. The training should use a variety of methods.
Measuring Training Effectiveness
Measuring the effectiveness of training programs is crucial for ensuring that they are meeting their objectives. The security auditor should help establish mechanisms for measuring training effectiveness, such as pre- and post-training assessments, quizzes, and employee surveys. The auditor should analyze the results of these assessments and use them to improve the training program and reinforce the message. This assessment also helps determine if more training is needed.
Responding to Data Privacy Incidents: Preparedness is Key
Despite the best efforts, data privacy incidents can occur. These incidents can range from minor data breaches to major data security incidents. Being prepared for such events is critical, and the security auditor plays a key role in developing and testing incident response plans. Preparedness is a critical component of a strong data privacy program.
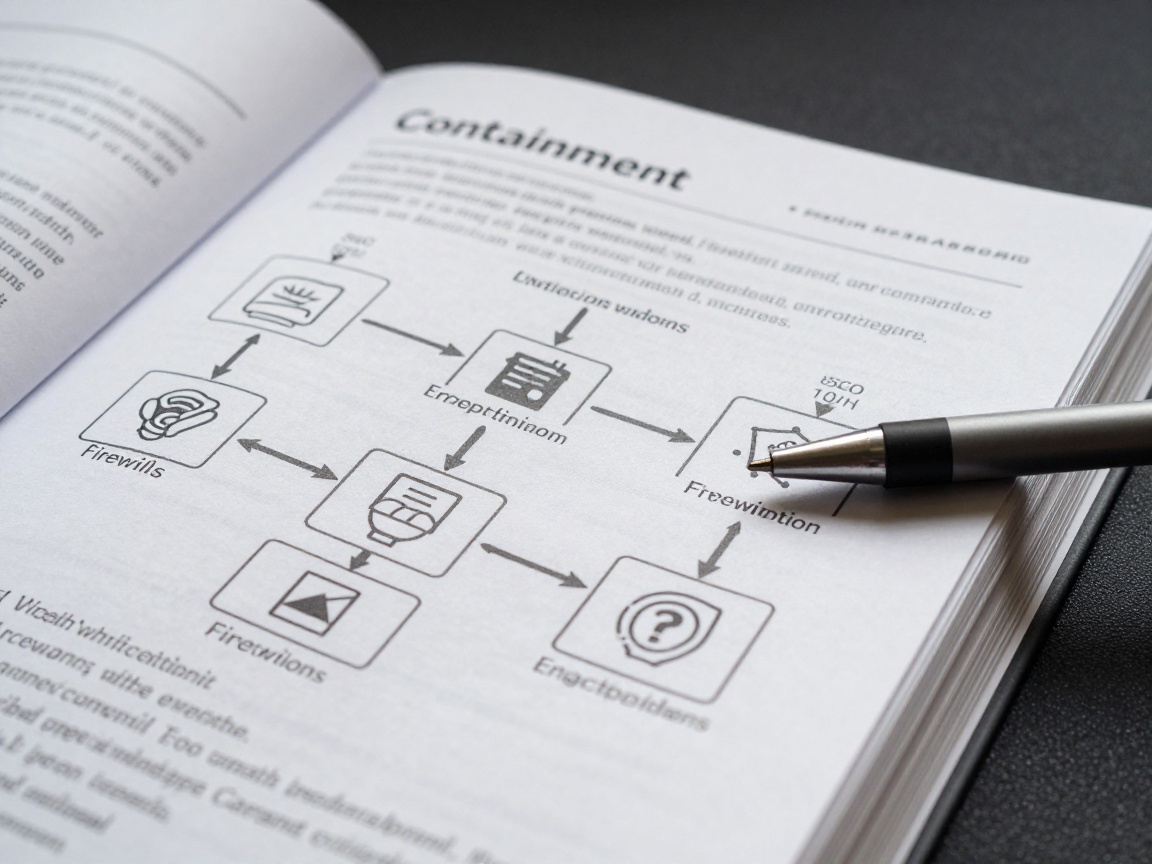
Incident Response Planning
A comprehensive incident response plan outlines the steps that an organization will take in the event of a data privacy incident. The security auditor should help develop the plan, defining roles, responsibilities, and procedures for detecting, containing, investigating, and recovering from incidents. They also should ensure that the plan is regularly reviewed, updated, and tested to ensure its effectiveness. A good plan is worthless if it is never reviewed.
Data Breach Notification Procedures
Data breach notification procedures are an essential component of the incident response plan. The security auditor should help establish procedures for notifying data subjects, regulatory authorities, and other stakeholders in the event of a data breach. The procedures should comply with all applicable regulatory requirements, including GDPR and CCPA. A good plan can limit the damage from an incident.
Staying Updated on Data Privacy Laws and Best Practices
The field of data privacy is constantly evolving. New regulations are emerging, and best practices are continuously refined. The security auditor must remain committed to continuous learning and professional development. This helps ensure their skills and knowledge remain up-to-date. It is imperative to stay current in this field.
Continuous Learning and Professional Development
Continuous learning is essential for staying current on data privacy laws and best practices. The security auditor should actively seek opportunities for professional development, such as attending conferences, obtaining certifications, and participating in training courses. They also should stay informed about industry trends and emerging threats. Professional development helps an auditor provide more relevant insights.
Leveraging Industry Resources and Communities
A wealth of resources are available to help security auditors stay informed about data privacy. This includes industry publications, online communities, and professional organizations. The security auditor should leverage these resources to stay up-to-date on the latest developments and exchange knowledge with peers. Knowledge of these sources can assist in the investigation.
Conclusion: The Future of Data Privacy and the Security Auditor
In conclusion, data privacy and protection is an ongoing and dynamic challenge, and security auditors are critical to maintaining compliance and building trust. As technology continues to evolve and the volume of data continues to grow, the role of the security auditor will become even more important. By mastering the concepts and practices outlined in this guide, security auditors can position themselves as invaluable contributors to their organizations’ data privacy efforts. The ability to adapt, learn, and remain vigilant will define the success of security auditors in this ever-changing landscape.
FAQs
-
What are the key responsibilities of a security auditor in data privacy?
A security auditor is responsible for conducting data privacy assessments, developing and reviewing data privacy policies, auditing data security controls, evaluating data processing agreements, monitoring data privacy compliance, assisting in training and awareness programs, and responding to data privacy incidents. -
What are the most important data privacy regulations that security auditors should be familiar with?
Security auditors should be familiar with key regulations such as GDPR, CCPA, HIPAA, and PIPEDA, as well as other relevant industry-specific regulations. -
How can a security auditor assess the effectiveness of data security controls?
Security auditors assess data security controls by reviewing access control mechanisms, evaluating the use of encryption, assessing network security configurations, and monitoring security events. -
What are the essential components of a data processing agreement?
Essential components of a data processing agreement include defining the scope of processing, specifying the types of data processed, outlining the purpose of processing, and specifying the vendor’s obligations regarding data security, data breach notification, and data subject rights. -
How can a security auditor stay updated on data privacy laws and best practices?
Security auditors can stay updated by continuously learning, attending industry conferences, obtaining certifications, and leveraging industry resources and communities.