Data Security & Privacy: The Security Architect’s Blueprint
Data is the lifeblood of the modern world, flowing through every industry and powering countless innovations. However, with this incredible value comes significant risk. Data breaches, privacy violations, and cyberattacks are constant threats, and that’s where the Security Architect comes in. They are the guardians, the strategic thinkers who build the defenses, set the policies, and guide the organization through the ever-changing landscape of data security and privacy. Let’s dive into the Security Architect’s world and explore their crucial role in protecting your data.
Introduction: The Security Architect – Data’s Guardian Angel
Picture a city with a complex network of infrastructure – roads, power grids, water systems. Protecting such a city requires a master planner, someone who understands the big picture and how all the pieces fit together. That’s the Security Architect in the realm of data. They are the strategic architects of digital security and privacy. They create the blueprints, design the defenses, and oversee the construction of a robust security posture that shields an organization’s valuable data assets from harm.
This role is not about simply installing firewalls or deploying antivirus software. It’s about understanding the business goals, the threat landscape, and how to build a security strategy that aligns with both. The Security Architect is the bridge between business needs and technical solutions, ensuring that security is not just a checkbox, but an integrated part of the entire organization. Their work is not just about preventing breaches; it’s about fostering a culture of security awareness and ensuring that data is handled responsibly and ethically.
Defining and Implementing Data Security Architecture
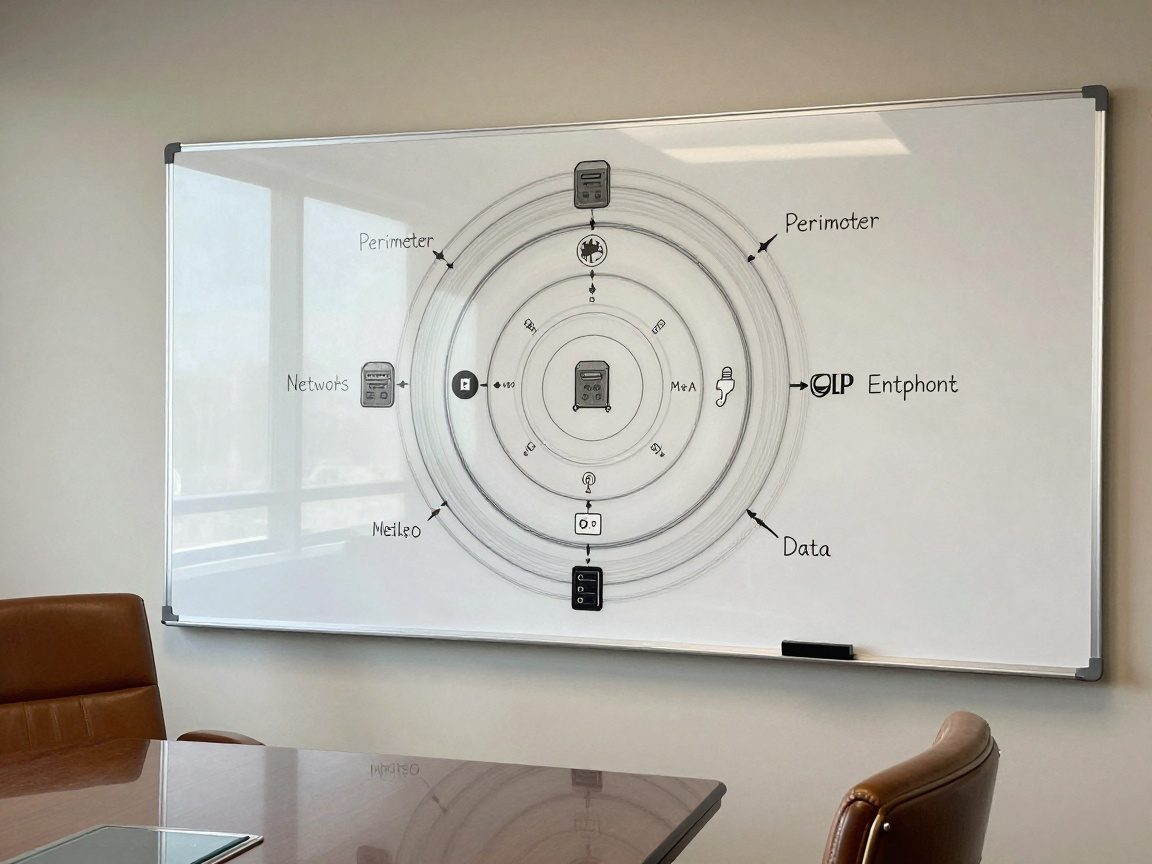
At the heart of the Security Architect’s role is defining and implementing a robust data security architecture. This involves creating a framework that addresses all aspects of data protection, from its creation and storage to its use and disposal. Think of it as designing the city’s defenses; the architect has to account for various threats, vulnerabilities, and the overall flow of citizens and goods (data).
Establishing the Foundation: Security Architecture Principles
Every great architecture starts with a set of core principles. For data security, these principles guide decision-making and ensure consistency across the organization. These might include:
- Defense in Depth: Implementing multiple layers of security, so if one layer fails, others are in place to protect the data.
- Least Privilege: Granting users only the minimum access necessary to perform their job functions.
- Zero Trust: Assuming no user or device is inherently trustworthy, and requiring verification before granting access to resources.
- Data Minimization: Collecting and retaining only the data necessary for business operations and nothing more.
- Privacy by Design: Integrating privacy considerations into the design and development of systems and processes from the outset.
These principles act as the building blocks for the entire security strategy, ensuring that every decision is aligned with the overall goals of data protection and privacy.
Designing for Defense: Data Security Architecture Components
The architecture itself is composed of various components that work together to safeguard data. Key components include:
- Access Controls: Implementing robust authentication and authorization mechanisms to control who can access data. This includes multi-factor authentication, role-based access control, and regular access reviews.
- Data Encryption: Encrypting data at rest and in transit to protect it from unauthorized access. This ensures that even if data is intercepted, it remains unreadable without the appropriate decryption keys.
- Network Security: Implementing firewalls, intrusion detection systems, and other network security measures to protect against external threats.
- Data Loss Prevention (DLP): Implementing DLP solutions to prevent sensitive data from leaving the organization’s control. This involves monitoring data movement and blocking unauthorized access.
- Security Information and Event Management (SIEM): Employing SIEM systems to collect and analyze security logs, detect threats, and respond to incidents in a timely manner.
The Security Architect selects and integrates these components to create a layered defense that addresses all potential attack vectors.
The Implementation Journey: Strategies and Best Practices
Implementing the data security architecture is a complex undertaking that requires careful planning and execution. Some effective strategies include:
- Risk-Based Approach: Prioritizing security efforts based on the most significant risks to the organization. This involves conducting risk assessments and focusing on the areas that pose the greatest threat.
- Automation: Automating security tasks to improve efficiency and reduce the risk of human error. This includes automating security configuration, vulnerability scanning, and incident response.
- Continuous Monitoring: Continuously monitoring the security environment to detect and respond to threats in real-time. This involves using SIEM systems, intrusion detection systems, and other monitoring tools.
- Documentation: Maintaining detailed documentation of the security architecture, including policies, procedures, and technical configurations. This helps with maintenance, auditing, and incident response.
- Training and Awareness: Providing regular training and awareness programs to educate employees about security threats and best practices.
Successful implementation requires a well-defined roadmap, strong collaboration across teams, and a commitment to continuous improvement.
Conducting Risk Assessments and Vulnerability Analysis
Before you can protect something, you need to know what you are protecting it from. That’s where risk assessments and vulnerability analysis come in. These are essential tasks for the Security Architect, allowing them to identify potential threats, assess vulnerabilities, and develop effective mitigation strategies. It is essentially understanding the enemy and their potential weapons.
Identifying the Threats: Types of Data Security Risks
The threat landscape is constantly evolving, so it is vital to stay informed about the latest threats and vulnerabilities. Common data security risks include:
- External Threats: Cyberattacks, such as malware, ransomware, phishing, and denial-of-service (DoS) attacks.
- Insider Threats: Malicious or unintentional actions by employees or contractors that can compromise data security.
- Physical Threats: Threats to physical infrastructure, such as natural disasters, theft, or unauthorized access to data centers.
- Compliance Risks: Failing to comply with data privacy regulations, such as GDPR, CCPA, and HIPAA.
- Operational Risks: Risks related to operational failures, such as software bugs, system outages, and data loss.
The Security Architect must be aware of these threats and understand how they might impact the organization’s data assets.
Unveiling Weaknesses: Vulnerability Assessment Techniques
Vulnerability analysis involves identifying weaknesses in systems, applications, and networks that could be exploited by attackers. Techniques include:
- Vulnerability Scanning: Using automated tools to scan systems and networks for known vulnerabilities.
- Penetration Testing: Simulating real-world attacks to identify vulnerabilities and assess the effectiveness of security controls.
- Code Reviews: Reviewing source code to identify security flaws and vulnerabilities.
- Configuration Audits: Auditing system and application configurations to ensure they are secure and meet security standards.
These techniques help the Security Architect identify weaknesses before they can be exploited by attackers.
Prioritizing Protection: Risk Mitigation Strategies
Once risks and vulnerabilities have been identified, the Security Architect must develop mitigation strategies to reduce the likelihood and impact of potential threats. These strategies include:
- Risk Avoidance: Eliminating the risk by discontinuing the activity or changing the business process.
- Risk Transfer: Transferring the risk to a third party, such as through insurance.
- Risk Mitigation: Reducing the likelihood or impact of the risk by implementing security controls.
- Risk Acceptance: Accepting the risk and taking no action. This is appropriate for low-impact risks that are unlikely to occur.
The Security Architect prioritizes mitigation efforts based on the severity of the risks and the cost-effectiveness of the controls.
… (The remainder would follow the same formatting ensuring markdown validity!)