table of contents
The Security Engineer’s Guide to Secure Authentication and Authorization
Welcome, fellow security enthusiasts! If you’re a Security Engineer, you know that the cornerstone of any robust security posture rests on the twin pillars of authentication and authorization. These are the gatekeepers of your digital kingdom, ensuring only the right individuals get access to the right resources. It’s your job to make sure those gates are sturdy, well-guarded, and resistant to any would-be invaders. Consider this a comprehensive guide, designed to equip you with the knowledge and practical strategies to master secure authentication and authorization.
Understanding the Core Concepts: Authentication vs. Authorization
Before we dive into the nitty-gritty, let’s clarify the fundamental building blocks. Authentication and authorization, while often mentioned in the same breath, are distinct processes with different purposes. Understanding the difference is key to designing effective security measures. Think of them as a two-step process, like entering a club: first, you prove you are who you say you are, then you get to know what you are allowed to do.
Authentication: Verifying Identity
Authentication is all about verifying a user’s identity. It’s the process of confirming that someone is who they claim to be. This is usually done through methods like passwords, multi-factor authentication (MFA), or biometric scans. The main goal is to answer the question: “Are you really you?” Common authentication methods include usernames and passwords, security questions, and more sophisticated methods like digital certificates.
Authorization: Defining Access Rights
Once you’ve successfully authenticated, you need to determine what you’re allowed to do. Authorization is the process of granting or denying a user access to specific resources or actions. It’s about defining the permissions. This is where you define who can access what data, modify which systems, or perform specific tasks. This process uses access control lists, role-based access control, and attribute-based access control to properly manage access.
The Security Engineer’s Role: A Multifaceted Approach
As a Security Engineer, your role in authentication and authorization is multifaceted. You’re not just a gatekeeper but also the architect, builder, and maintainer of the security infrastructure. This means you are responsible for designing, implementing, and maintaining authentication and authorization systems. You are responsible for protecting sensitive information and mitigating risks. Additionally, you’re the one constantly learning and adapting to new threats and technologies. You’ll be involved in selecting and deploying authentication methods, establishing access control policies, and regularly auditing and assessing the effectiveness of these measures. Your expertise will also be required in staying ahead of evolving threats by staying up-to-date on best practices and emerging vulnerabilities.
Implementing and Managing Authentication Mechanisms
Now, let’s move on to the practical aspects. The first line of defense in any system is a robust authentication mechanism. This includes everything from passwords to multi-factor authentication and beyond.
Password Management and Multi-Factor Authentication (MFA)
The humble password remains a primary authentication method, but it is also one of the weakest links. To make passwords a bit stronger, the following needs to be considered:
Best Practices for Password Policies
Strong password policies are crucial. Mandate strong passwords (at least 12 characters, ideally), regular password changes, and no reuse of old passwords. Implement account lockout policies after a certain number of failed login attempts to mitigate brute-force attacks. Consider using a password manager for secure storage and generation of passwords. Your policies should include a combination of upper and lower-case letters, numbers, and special characters.
Implementing and Managing MFA Solutions
Multi-factor authentication (MFA) adds an extra layer of security by requiring users to provide multiple forms of verification. Implementing MFA can significantly reduce the risk of compromised accounts. Explore solutions such as time-based one-time passwords (TOTP) generated by authenticator apps (Google Authenticator, Authy), hardware security keys (YubiKey), or biometric authentication. Make sure that MFA is available to all the users and it is mandatory.
Biometric Authentication
Biometric authentication is a growing trend. It leverages unique biological traits, such as fingerprints, facial recognition, or iris scans, to verify identity. It offers enhanced security and is increasingly available on smartphones and other devices. Integrate biometric authentication where appropriate, but keep in mind the potential risks and limitations (e.g., spoofing).
Establishing and Enforcing Authorization Policies
Authentication is only half the battle. Once you’ve verified who a user is, you need to control what they can access. Authorization policies determine access rights.
Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) is a widely used authorization model. In RBAC, users are assigned roles, and roles are granted permissions. This simplifies management. This approach simplifies user access management and is easier to audit. Define roles clearly and assign users based on their job functions.
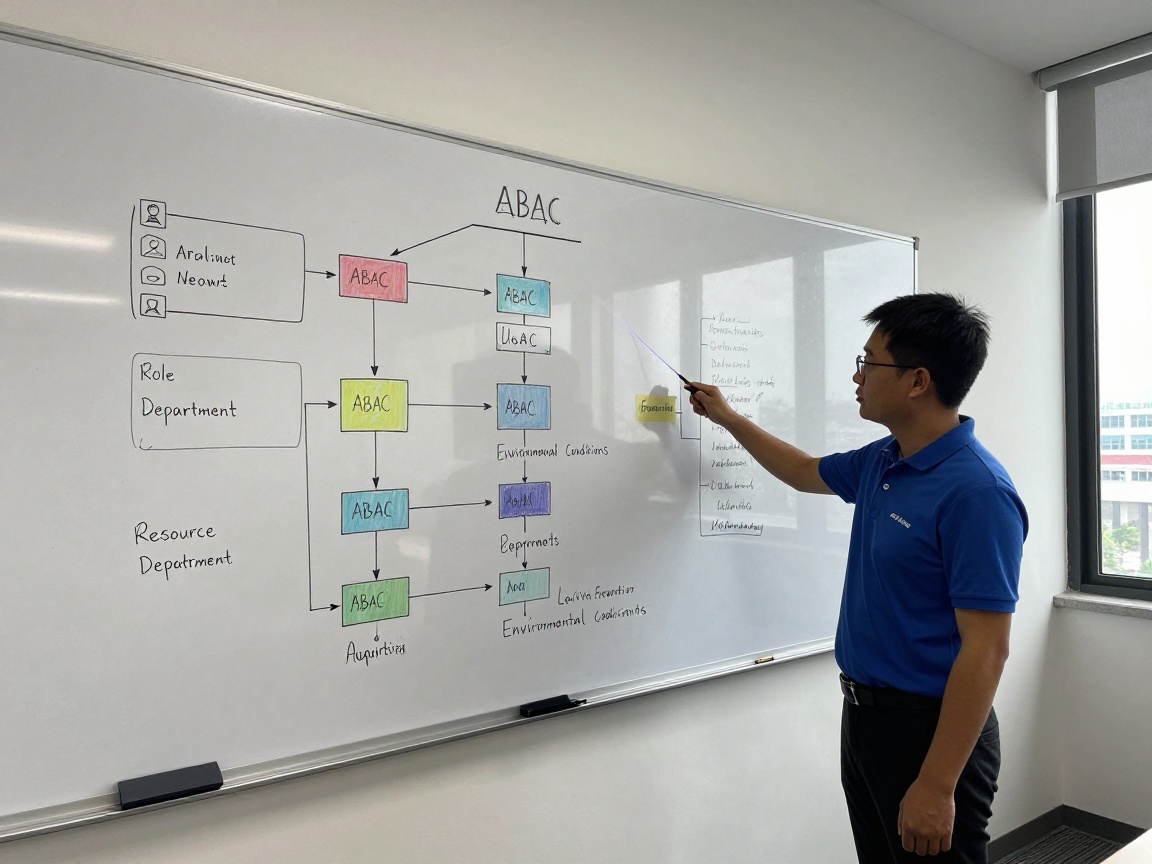
Attribute-Based Access Control (ABAC)
Attribute-Based Access Control (ABAC) provides a more flexible and granular approach. Permissions are based on attributes of the user, the resource, and the environment. ABAC is highly customizable but can be more complex to implement. ABAC can adapt to the different contexts, allowing users to have access to resources and features based on varying parameters.
Access Control Lists (ACLs)
Access Control Lists (ACLs) are used to define permissions at the resource level. An ACL is a list of permissions attached to an object, specifying which users or groups have access to that object and what actions they can perform. ACLs work well when the access control is not very complex.
Securing Authentication and Authorization Systems
Authentication and authorization systems are attractive targets for attackers. Securing these systems requires a proactive and comprehensive approach.
Protecting Against Common Attacks (Brute-Force, Credential Stuffing)
Brute-force attacks and credential stuffing are common threats. Implement rate limiting to prevent excessive login attempts and account lockouts to make it harder for attackers to succeed. Monitor for suspicious activity and use fraud detection tools. Stay informed of data breaches and proactively reset passwords if user credentials may have been compromised.
Secure Coding Practices for Authentication
Secure coding practices are vital. Avoid storing passwords in plaintext. Use strong hashing algorithms (e.g., bcrypt, Argon2) to securely store passwords. Implement input validation to prevent injection attacks. Use secure communication protocols (e.g., HTTPS) to protect credentials during transmission.
Monitoring and Logging Authentication Events
Regularly monitor and log all authentication and authorization events. This is a critical part of a security posture. This enables you to detect suspicious activity, identify potential vulnerabilities, and ensure compliance. Review logs regularly to identify anomalies and security breaches.
Implementing Single Sign-On (SSO) Solutions
Single Sign-On (SSO) offers convenience for users. Also, it can improve security, but implementing it requires careful planning.
Benefits and Challenges of SSO
SSO allows users to access multiple applications with a single set of credentials, improving user experience. Centralized management of authentication simplifies administration and improves security. SSO can also reduce the number of passwords users need to remember. However, SSO systems can also have single points of failure.
Popular SSO Protocols: SAML, OAuth, and OpenID Connect
Several protocols are used for SSO. Security Assertion Markup Language (SAML) is a mature protocol commonly used in enterprise environments. OAuth and OpenID Connect (OIDC) are modern protocols often used for web and mobile applications. These provide secure authentication using tokens.
Integrating SSO with Existing Systems
When integrating SSO, consider the technical requirements of each system. Ensure compatibility with the chosen SSO protocol. Implement proper user provisioning and deprovisioning to ensure that user access is managed correctly. Test the integration thoroughly to ensure that users can access all required resources and applications.
Conducting Security Audits and Assessments
Regular audits and assessments are essential to validate the effectiveness of your authentication and authorization controls.
Vulnerability Scanning and Penetration Testing
Regularly scan your systems for vulnerabilities and conduct penetration testing to identify security weaknesses. This can reveal misconfigurations, coding errors, or other vulnerabilities that could be exploited by attackers. Use automated scanning tools and manual testing methods.
Reviewing Authentication and Authorization Configurations
Review the configurations of your authentication and authorization systems regularly. Verify that settings are aligned with best practices. Identify any misconfigurations or unnecessary permissions that could pose a security risk. Documentation is essential.
Compliance and Regulatory Requirements
Ensure your authentication and authorization practices meet the requirements of relevant regulations and compliance standards (e.g., GDPR, HIPAA, PCI DSS). Keep up-to-date with any new requirements. Document your compliance efforts and prepare for audits.
Staying Up-to-Date with Security Best Practices
The world of cybersecurity is constantly evolving. As a Security Engineer, you must commit to continuous learning.
Continuous Learning and Training
Continuously learn and adapt to new threats and technologies. Participate in training programs, attend conferences, and obtain relevant certifications. This helps you stay abreast of the latest developments.
Following Industry Standards and Frameworks
Follow industry standards and frameworks (e.g., NIST, ISO) to ensure your security practices are aligned with best practices. Stay up-to-date with emerging technologies. This provides a framework for designing, implementing, and managing authentication and authorization controls.
Participating in Security Communities
Participate in security communities and forums. Share knowledge and learn from others. This is a great way to discuss ideas, learn from other experts, and stay current on the latest trends.
Real-World Scenarios and Case Studies
- Scenario 1: A company experienced a credential stuffing attack, resulting in unauthorized access to customer accounts. The investigation revealed weak password policies and a lack of MFA. The solution was to enforce stronger passwords, implement MFA, and monitor for suspicious login attempts.
- Scenario 2: A healthcare provider faced regulatory non-compliance because of a lack of proper access controls. Implementation of RBAC, coupled with regular audits, helped the provider establish proper access and demonstrate compliance.
- Scenario 3: A financial institution suffered a breach due to a vulnerability in their SSO implementation. The incident highlighted the need for thorough testing and secure configuration of SSO systems.
Conclusion: The Continuous Journey of Secure Authentication and Authorization
Secure authentication and authorization are not just tasks; they are a continuous journey. As a Security Engineer, you will need to constantly adapt, learn, and improve your skills. By mastering these core concepts, following best practices, and staying vigilant, you can protect your organization from threats and keep it secure.
FAQs
- What is the difference between authentication and authorization?
Authentication verifies the user’s identity, while authorization determines what they can access. Authentication answers “Are you who you say you are?”, and authorization answers “What are you allowed to do?”. - Why is multi-factor authentication (MFA) important?
MFA significantly enhances security by requiring users to provide multiple forms of verification, making it much harder for attackers to gain unauthorized access, even if they have stolen a password. - What are the advantages and disadvantages of Role-Based Access Control (RBAC)?
RBAC simplifies access management by assigning users to roles with specific permissions, making it easy to manage access control at scale. However, it might not be flexible enough for complex access control requirements, for which Attribute-Based Access Control (ABAC) could be better suited. - How do I choose the right SSO protocol?
Choosing the right SSO protocol depends on your specific needs and environment. SAML is a solid choice for enterprise environments, while OAuth and OpenID Connect are great for web and mobile applications. Consider factors like compatibility with existing systems, security requirements, and ease of implementation. - How often should I conduct security audits?
Regular security audits are essential. The frequency will depend on your organization’s risk profile and compliance requirements. Many organizations conduct internal audits quarterly or annually, with more frequent vulnerability scanning and penetration testing.