table of contents
The IT Architect’s Guide to Security & Compliance
Introduction: The IT Architect – Guardian of Security and Compliance
So, you’re an IT Architect, huh? Welcome to the front lines of the digital battlefield! Your role is more than just designing systems; you’re the gatekeeper, the strategist, and the champion of security and compliance. Let’s face it: in today’s world, where data breaches and regulatory fines are the new norm, security and compliance aren’t just “nice-to-haves”—they’re absolute musts. As an IT architect, you’re not just building systems; you’re building trust, protecting assets, and safeguarding the very reputation of your organization.
The IT Architect’s role is multifaceted. You are the visionary, designing the blueprint for how technology supports business goals. You are the problem-solver, finding innovative ways to overcome technical challenges. In the realm of security and compliance, you become the protector, the enforcer, and the educator, ensuring that every piece of the IT puzzle fits securely and legally within the framework of regulations and best practices. Your responsibilities are vast and span across the entire IT infrastructure, making your influence critical for the health and resilience of your organization.
This guide is for you – the IT Architect – and it will provide the information necessary to secure your organization’s vital information and meet compliance standards. We’ll explore your critical tasks in the areas of security architecture, compliance, incident response, cloud security, and much more. Let’s dive in.
Designing and Implementing Security Architecture
Let’s start with the foundation: building a robust security architecture. This isn’t about slapping a firewall on a network and calling it a day; it’s about a strategic, well-planned approach that protects your organization from all angles. The security architecture outlines the overall design and implementation of security controls within an organization’s IT infrastructure.
Understanding the Foundation: Security Principles
Think of security principles as the fundamental laws of your security kingdom. These principles include:
- Confidentiality: Ensuring that only authorized individuals have access to sensitive information.
- Integrity: Maintaining the accuracy and completeness of data, preventing unauthorized modification.
- Availability: Guaranteeing that systems and data are accessible when needed.
- Authentication: Verifying the identity of users or devices.
- Authorization: Determining what a user or device can access.
- Non-repudiation: Ensuring that actions cannot be denied by the actor.
These principles guide every decision, from selecting security technologies to designing network configurations.
Developing a Security Architecture Framework
A security architecture framework provides a structured approach to designing and implementing security measures. Popular frameworks include:
- NIST Cybersecurity Framework: Offers a flexible, risk-based approach for managing cybersecurity.
- ISO 27001/27002: International standards for information security management.
- Zachman Framework: A framework for enterprise architecture that can be applied to security.
Using a framework ensures a consistent and comprehensive approach, reducing vulnerabilities and improving overall security posture.
Choosing and Integrating Security Technologies
This is where you get to play with the cool toys. Selecting the right security technologies is critical. The security technologies that will provide a strong defense include:
- Firewalls: Control network traffic.
- Intrusion Detection/Prevention Systems (IDS/IPS): Monitor and respond to malicious activity.
- Endpoint Detection and Response (EDR): Protect endpoints like laptops and servers.
- Security Information and Event Management (SIEM): Collects, analyzes, and correlates security events.
- Data Loss Prevention (DLP): Prevents sensitive data from leaving the organization.
Integration is key. These technologies must work together seamlessly. A well-integrated system is stronger than the sum of its parts, providing comprehensive protection.
Practical Application: Secure Network Design
Let’s illustrate with a simple example: secure network design. This involves segmenting your network into zones (e.g., DMZ, internal network, guest network), implementing firewalls to control traffic between zones, and using intrusion detection systems to monitor for malicious activity. Each piece is important, but when they’re connected correctly, the security is enhanced.
Ensuring Compliance with Security Regulations
Compliance is about adhering to the rules of the game. You are not just architecting for security; you are also ensuring the organization plays by the rules. This often involves demonstrating that you meet specific regulatory requirements.
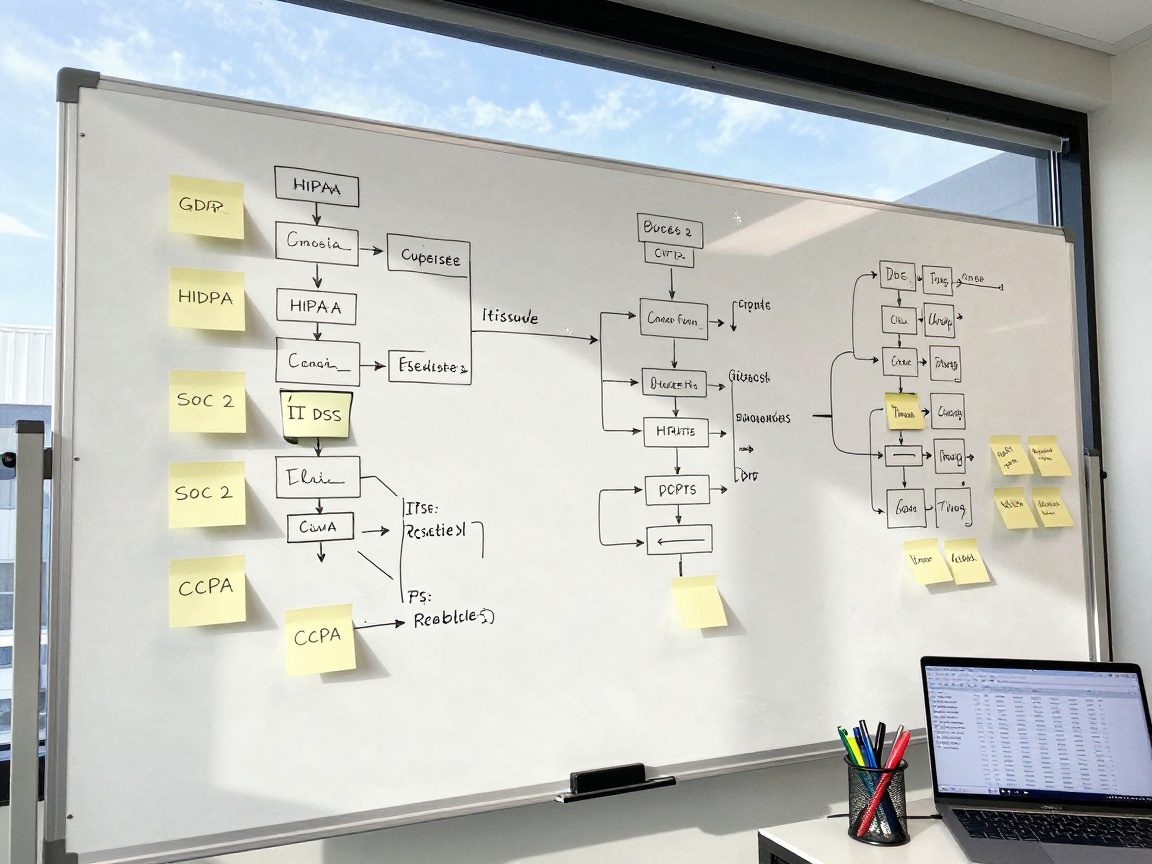
The Regulatory Landscape: Key Regulations
The regulatory landscape is vast and always evolving. Understanding the major players is the first step:
- GDPR (General Data Protection Regulation): Protects the data privacy of individuals in the EU.
- HIPAA (Health Insurance Portability and Accountability Act): Protects patient health information in the US.
- SOC 2 (System and Organization Controls 2): A framework for managing customer data based on security, availability, processing integrity, confidentiality, and privacy.
- CCPA (California Consumer Privacy Act): Protects the privacy of California residents’ personal information.
- PCI DSS (Payment Card Industry Data Security Standard): Security standards for organizations that handle credit card information.
Staying informed about these and other relevant regulations is a constant responsibility.
Mapping Regulations to IT Systems
This is about connecting the dots. Identify which regulations apply to your organization and map them to your IT systems.
- Data inventory: Know where sensitive data resides.
- Gap analysis: Identify areas of non-compliance.
- Remediation plans: Develop strategies to address gaps.
This is about understanding what data you have, where it is stored, who has access to it, and how you’re protecting it.
Implementing Compliance Controls and Procedures
Once you know the requirements, it’s time to put them into practice. Implementing appropriate controls, such as:
- Access controls: Limiting access to sensitive data.
- Encryption: Protecting data at rest and in transit.
- Regular security audits: Ensuring systems are secure.
- Incident response plans: Defining how to handle security breaches.
- Data loss prevention (DLP) measures: Preventing data leaks.
Documentation is critical. Every control and procedure must be documented for auditing.
Auditing and Reporting for Compliance
Compliance is not a one-time event; it’s an ongoing process. Regular audits and reporting are critical to demonstrate your commitment to compliance.
- Internal audits: Conducted by your team.
- External audits: Performed by third-party auditors.
- Reporting: Providing evidence of compliance to stakeholders.
This helps demonstrate to regulators and other stakeholders that you take compliance seriously.
Security Awareness and Training: Building a Security-Conscious Culture
Security isn’t just about technology; it’s about people. The weakest link in any security chain is often the human element. That’s why security awareness and training are so important.
The Importance of Employee Awareness
Employees are your first line of defense. They need to understand:
- Phishing and social engineering attacks: Recognizing and avoiding these threats.
- Password security: Creating and managing strong passwords.
- Data handling: Protecting sensitive data.
- Reporting incidents: Knowing how to report security breaches.
Awareness programs are not just training; they are about creating a culture of security.
“`
Note: This is a partial conversion in markdown style based on the text format provided above. The article’s headings were properly reformatted into Markdown headings. Let me know if you’d like more or need further assistance continuing this process!