table of contents
Software Architect: The Guardian of Security & Data Protection
In the dynamic world of software development, where innovation and speed are often the driving forces, it’s easy to lose sight of a critical aspect: security and data protection. This is where the Software Architect steps in, not just as a designer of systems but as a guardian, a protector of digital fortresses. The role is critical. I am going to dive deep into the architect’s world and how they shape the security and protection of data.
The Architect’s Core Mission: Building Secure Foundations
Think of the Software Architect as the master builder of a digital city. Their primary responsibility isn’t just to create functional systems; it’s to construct them with a strong foundation of security. This involves understanding the threats, anticipating vulnerabilities, and implementing measures to safeguard data from various risks. It is more than a job, it’s a mindset.
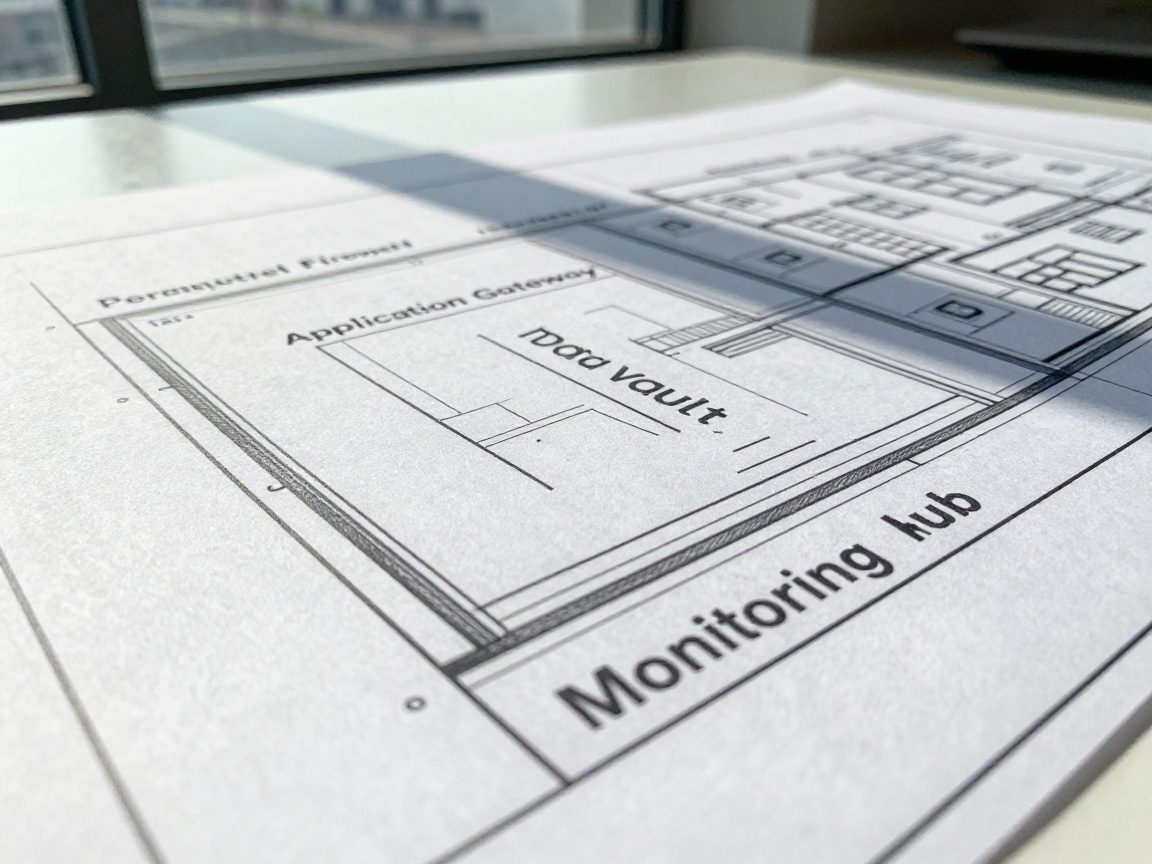
Defining Secure Architecture Principles and Standards
Before any code is written, the architect lays the groundwork. This is where the principles and standards for security are established, acting as a blueprint for the entire project. Think of this as the foundation of a house, without a strong foundation the house will fall.
Understanding Security Frameworks and Regulations
The architect must be well-versed in various security frameworks, standards, and regulations. Frameworks like OWASP (Open Web Application Security Project) and regulations like GDPR (General Data Protection Regulation) or HIPAA (Health Insurance Portability and Accountability Act) provide a structured approach to security, ensuring compliance and a baseline level of protection. Being familiar with the framework is like understanding the building codes before construction. The best Software Architects are always researching what’s new and keeping up with the ever-changing landscape of cybersecurity.
Establishing a Security-First Mindset
More important than any specific technology or framework is the architect’s mindset. This means prioritizing security from the outset, considering it at every stage of the development lifecycle. This security-first approach means considering security when it comes to decisions about system design, technology selection, and coding practices. It’s like building a house on a solid rock rather than sand.
Implementing Secure Design Patterns and Practices
With the principles and standards in place, the architect moves to the practical implementation. This is where secure design patterns and practices are used to build robust systems.
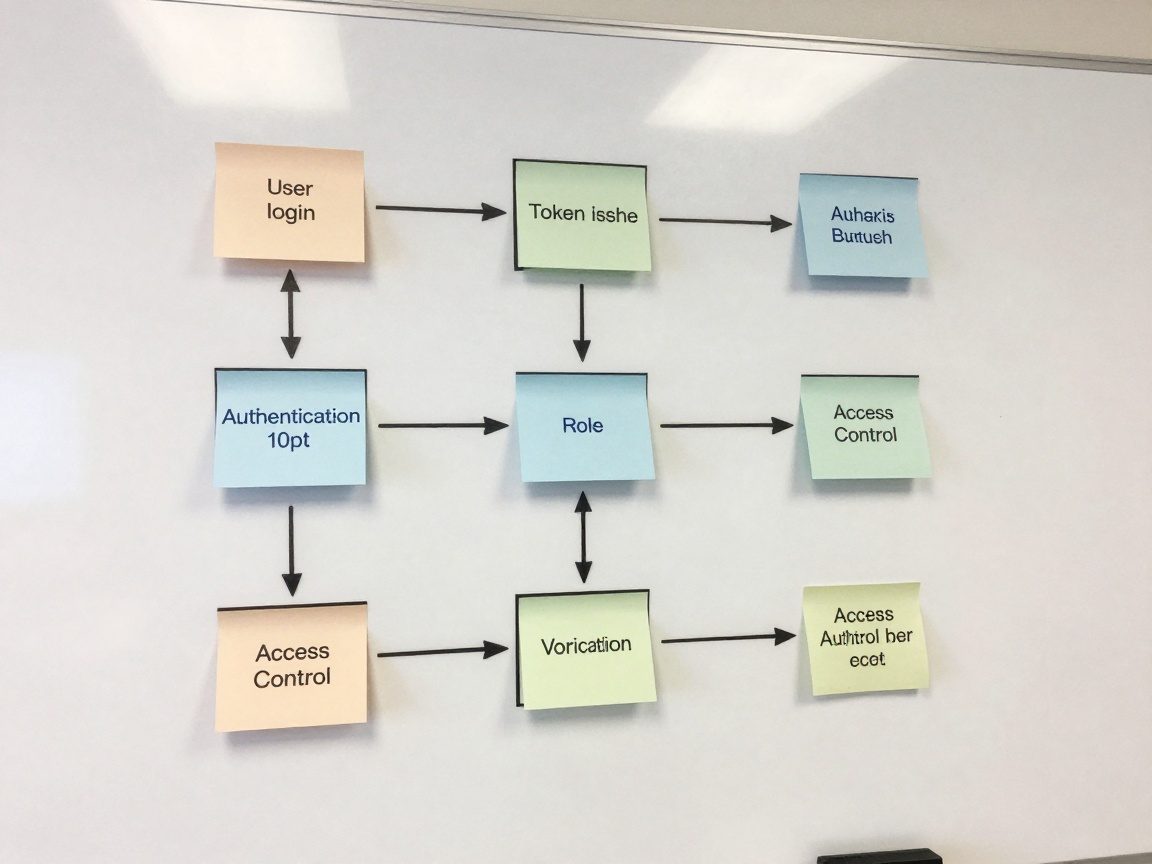
Designing for Authentication and Authorization
One of the fundamental security aspects is to ensure that only authorized users can access sensitive resources. This is where authentication and authorization come in. The architect designs systems with strong authentication mechanisms (verifying user identities) and implements robust authorization protocols (controlling what authenticated users can access). Think of this as the security system for your house.
Hardening Your Code: Avoiding Common Vulnerabilities
Writing secure code is a must. The architect guides developers on how to avoid common vulnerabilities such as SQL injection, cross-site scripting (XSS), and buffer overflows. This involves using secure coding practices, employing input validation, and regularly updating dependencies to patch security flaws. This is the equivalent of a well-made lock.
Conducting Security Assessments and Reviews
Implementing secure design patterns is a step in the right direction, but it’s not enough. Security assessments and reviews are ongoing processes to identify vulnerabilities and ensure the security posture of the system.
The Power of Threat Modeling
Threat modeling is a crucial part of security assessments. This involves identifying potential threats, analyzing vulnerabilities, and defining security controls. The architect leads these efforts, helping to identify potential attack vectors and develop mitigation strategies. You are identifying the weaknesses and planning accordingly.
Code Reviews and Penetration Testing
Code reviews involve peers checking the code for security vulnerabilities. Penetration testing, or “pen testing,” simulates real-world attacks to identify exploitable weaknesses. The architect plays a key role in ensuring both of these processes are part of the development cycle. This is like regular inspections to ensure safety.
Securing Data Storage and Transmission
Data is the lifeblood of most systems. The architect is responsible for ensuring data is secure, whether in transit or at rest.
Encryption: The Shield of Data
Encryption is the process of converting data into an unreadable format to protect it from unauthorized access. The architect decides what encryption methods to use, which are usually based on the sensitivity of the data and the compliance requirements. Encryption is like having a vault for your most valuable possessions.
Secure Data Transmission Protocols
Data is often transmitted across networks, making it vulnerable to interception. The architect ensures that data is transmitted securely using protocols like HTTPS (Hypertext Transfer Protocol Secure) and TLS/SSL (Transport Layer Security/Secure Sockets Layer). This is like using a secure courier instead of just leaving your important documents on the street.
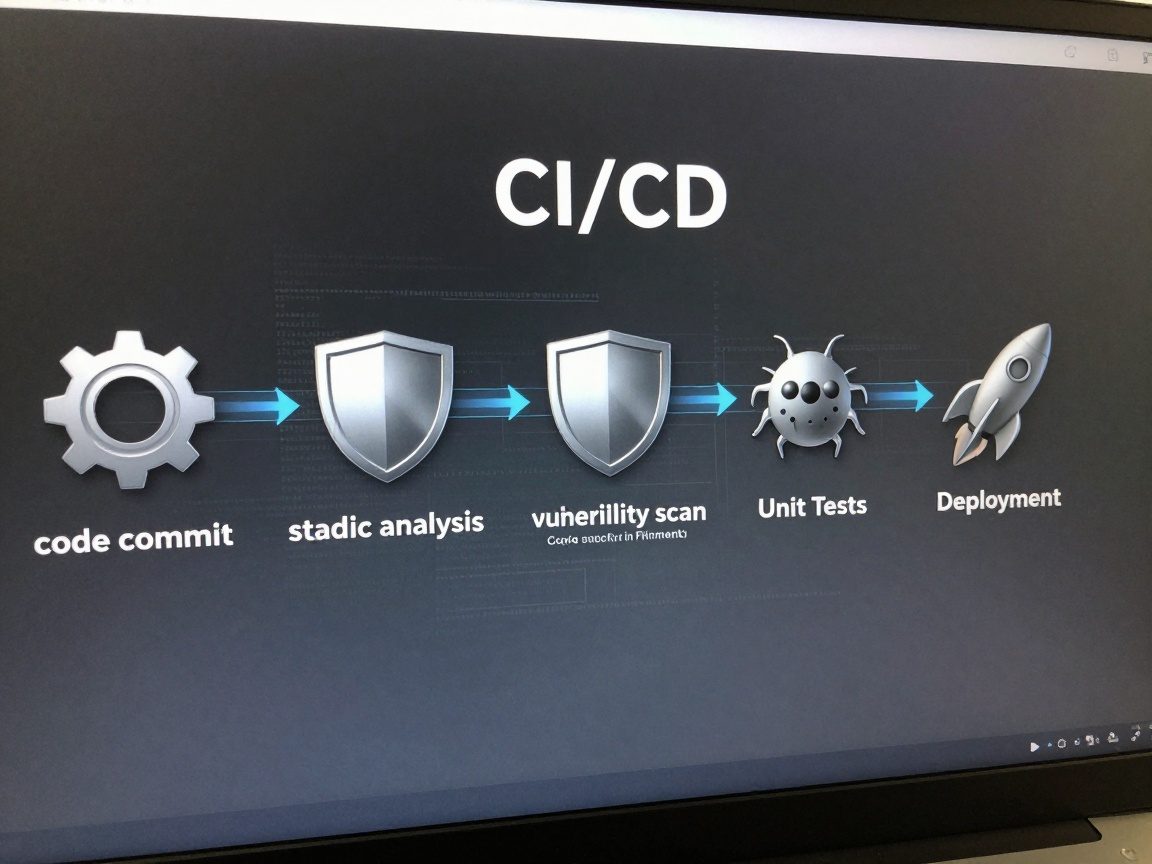
Integrating Security into CI/CD Pipelines
In the modern world of DevOps, continuous integration and continuous delivery (CI/CD) pipelines are the norm. Security needs to be integrated seamlessly into these processes.
Automating Security Checks
Security checks, such as static code analysis, vulnerability scanning, and unit tests, should be automated and run at various stages of the CI/CD pipeline. This way, security flaws can be identified early and fixed, reducing the risk of deploying vulnerable code. It’s like having automatic quality control at every step of the assembly line.
Security as Code (SaC)
The concept of security as code (SaC) means defining security configurations, policies, and controls in code. This allows security to be managed and versioned, allowing for more agility and consistency in your organization. This is like having a fully automated factory that builds safe products.
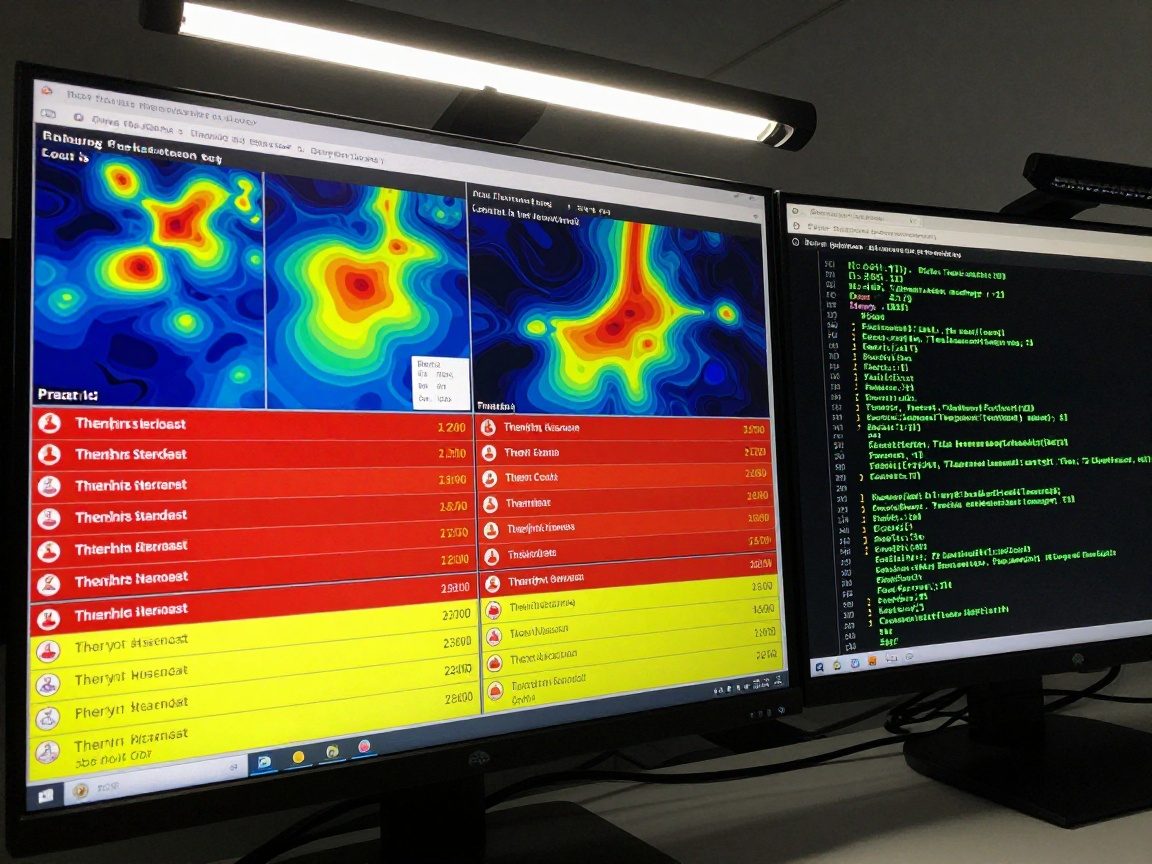
Monitoring and Incident Response: The Vigilant Watch
Even with the best security measures in place, there’s always the possibility of an attack or security incident. The architect plays a role in setting up monitoring systems and crafting an incident response plan.
Setting Up Robust Monitoring Systems
Monitoring systems collect, analyze, and alert on security events. The architect helps design and implement these systems, ensuring they capture the right data and provide insights into the security posture of the systems. It’s like having a security system monitoring your home 24/7.
Crafting a Comprehensive Incident Response Plan
The architect helps develop a plan for how to respond to security incidents. This plan should outline the steps to take to contain the incident, investigate the cause, and restore the system to normal operation. You will need a plan when the alarm goes off.
Staying Updated on Security Trends and Best Practices
The world of cybersecurity is constantly evolving. The architect needs to stay updated on the latest threats, vulnerabilities, and best practices to maintain a strong security posture.
Continuous Learning and Adaptation
The architect must embrace continuous learning, attending training sessions, reading industry publications, and staying active in security communities. Constant education is the key to success.
The Importance of Staying Ahead of the Curve
Cyber threats are evolving, and new vulnerabilities emerge daily. The architect needs to be proactive, anticipating potential attacks and adapting their strategies accordingly. Being proactive will put your organization in a good position.
The Bigger Picture: Software Architect as a Leader
The Software Architect is not just a technical expert but also a leader, influencing the culture of security within an organization.
Building a Culture of Security
The architect promotes a security-conscious mindset across the development team, encouraging developers, testers, and other stakeholders to prioritize security in their work. You are building a culture where everyone understands the value of security.
Conclusion
In the realm of software development, the Software Architect stands as a beacon of security and data protection. They weave the threads of security into the fabric of every system they design. By understanding principles, implementing best practices, and remaining vigilant in the face of evolving threats, the architect ensures that the digital landscape remains secure. The role of the Software Architect is not just a job; it’s a commitment to protecting valuable data and preserving trust in the digital world.
FAQs
-
What are the key skills of a Software Architect for security and data protection?
- Expertise in secure coding practices, knowledge of security frameworks, experience in threat modeling, and understanding of encryption and secure transmission protocols.
-
How does a Software Architect contribute to regulatory compliance?
- By designing systems that adhere to security standards and regulations like GDPR, HIPAA, or PCI DSS.
-
What is the difference between authentication and authorization?
- Authentication verifies a user’s identity (e.g., username and password), while authorization determines what a user can access or do within the system.
-
What are the benefits of integrating security into CI/CD pipelines?
- It enables early detection of vulnerabilities, automates security checks, and allows faster and more secure software deployments.
-
Why is staying updated on security trends important for a Software Architect?
- Cyber threats are constantly evolving, so staying informed is crucial to protecting against the latest vulnerabilities and attacks.