table of contents
Threat Intelligence & Monitoring: The Security Architect’s Strategic Arsenal
In today’s ever-evolving digital landscape, the role of a Security Architect is more critical than ever. They are the guardians of an organization’s digital kingdom, responsible for designing, implementing, and maintaining the defenses against a relentless tide of cyber threats. Two key pillars that form the foundation of this defensive strategy are threat intelligence and monitoring. These elements provide the architect with the visibility and knowledge needed to anticipate, detect, and respond to attacks effectively. This article will explore these crucial areas, providing a roadmap for Security Architects looking to fortify their organization’s security posture.
Introduction: Why Threat Intelligence and Monitoring Matter
Imagine trying to defend a castle without knowing where the enemy might strike or what weapons they might employ. That’s the reality of cybersecurity without threat intelligence and effective monitoring. Threat intelligence provides the “know-how” – the insights into attackers’ tactics, techniques, and procedures (TTPs), and the vulnerabilities they exploit. Monitoring provides the “eyes and ears” – the constant vigilance, detecting suspicious activity and potential breaches. In essence, threat intelligence informs the “what” and “why,” while monitoring focuses on the “how” and “when.” These two functions are inextricably linked, and the success of a security program hinges on their effective integration. A Security Architect that can master these two concepts will be well on their way to becoming a leader in their field.
Defining the Core of Threat Intelligence and Monitoring
Before diving into the Security Architect’s specific tasks, let’s clarify the fundamental components of threat intelligence and monitoring.
Understanding Threat Intelligence
Threat intelligence is more than just a collection of indicators of compromise (IOCs); it’s a dynamic process of gathering, analyzing, and disseminating information about existing and emerging threats. It involves understanding the threat landscape, identifying potential risks, and proactively preparing for attacks. This includes information about threat actors, their motivations, the tools and techniques they use, and the targets they are likely to pursue. The goal is to move from a reactive to a proactive defense, anticipating attacks before they occur. Consider threat intelligence as a spyglass that Security Architects use to view the battlefield.
The Crucial Role of Security Monitoring
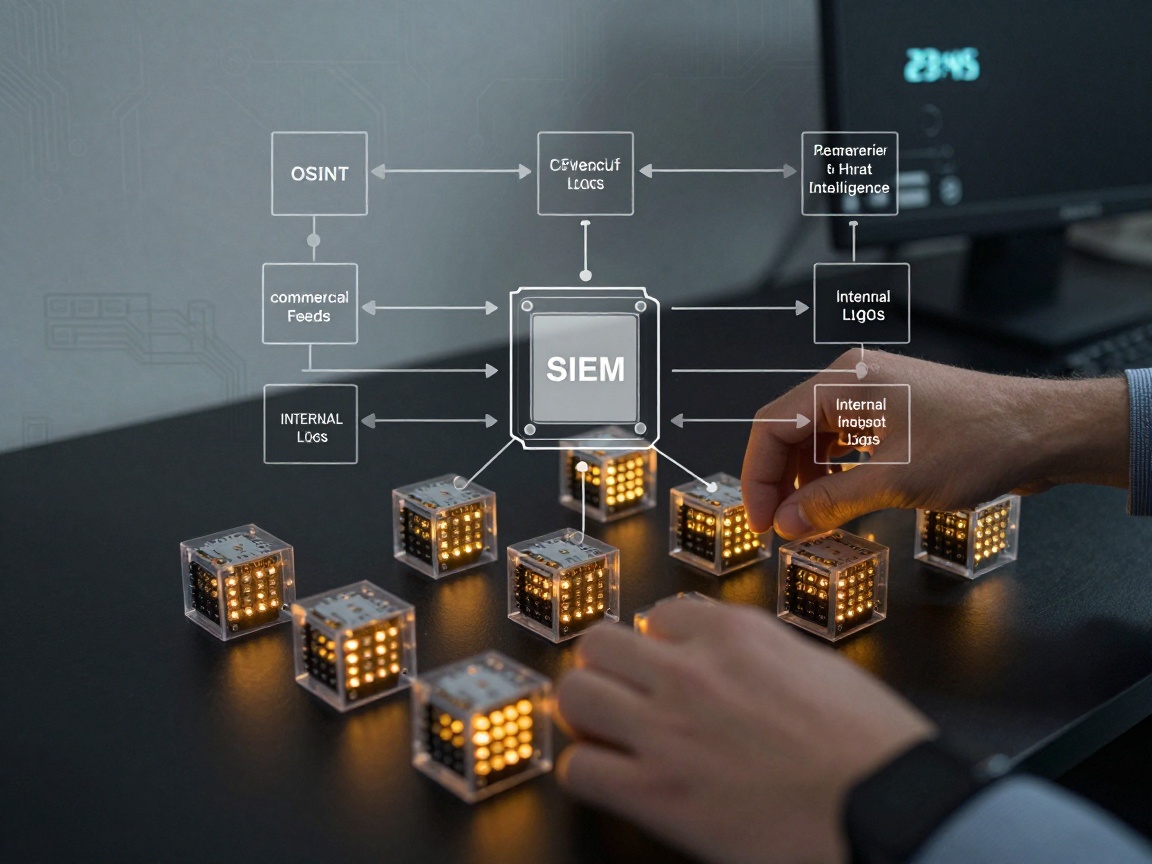
Security monitoring involves the continuous collection, analysis, and interpretation of security-related data. This includes log data from systems, network traffic, and endpoint activity. It aims to detect anomalies, identify potential security incidents, and provide timely alerts to security teams. Effective monitoring is the vigilant watchman, constantly observing and reporting any suspicious behavior. It often relies on tools like Security Information and Event Management (SIEM) systems to aggregate and analyze data from various sources, providing a centralized view of the security posture.
The Security Architect’s Responsibilities: A Deep Dive
The Security Architect plays a pivotal role in implementing and maintaining these crucial security functions. Let’s delve into the specific tasks that define this role.
Developing and Maintaining Threat Intelligence Feeds
This is where the Security Architect builds the “intelligence network.”
Sources of Threat Intelligence: Where to Look
The landscape of threat intelligence is vast, with various sources providing valuable information. These include:
- Commercial Threat Intelligence Feeds: Services from providers like Recorded Future, CrowdStrike, and Mandiant offer curated threat data and analysis.
- Open-Source Intelligence (OSINT): Freely available information from blogs, social media, forums, and public databases.
- Internal Intelligence: Information gathered from an organization’s security logs, incident response activities, and vulnerability assessments.
- Industry-Specific Information Sharing and Analysis Centers (ISACs): Collaboration with peers within your industry to share threat information and best practices.
Curating and Validating Threat Intelligence
Not all threat intelligence is created equal. Security Architects must carefully vet and validate the information they receive. This includes:
- Assessing the reliability of sources: Are they reputable? Is the data verified?
- Contextualizing the information: How does it apply to your organization?
- Prioritizing threats based on risk: Which threats pose the greatest danger?
Integrating Threat Intelligence with Security Tools
The real power of threat intelligence comes from its integration with security tools. This enables automated detection and response capabilities. Examples include:
- Integrating IOCs with SIEM: To detect malicious activity in logs.
- Feeding threat intelligence into firewalls: To block known malicious traffic.
- Using threat intelligence to inform vulnerability assessments: To prioritize patching efforts.
Building and Maintaining Security Monitoring Systems
This involves designing, implementing, and optimizing the organization’s “surveillance system.”
Designing a Robust Monitoring Architecture
A well-designed monitoring architecture should consider:
- Comprehensive Data Sources: Collecting logs from servers, networks, endpoints, and applications.
- Scalability: Ensuring the system can handle increasing data volumes.
- Performance: Minimizing impact on system performance.
- Resilience: Designing for high availability and fault tolerance.
Implementing Security Information and Event Management (SIEM) Systems
SIEM systems are the heart of the monitoring infrastructure. They aggregate logs, correlate events, and provide analytics for security teams. The Security Architect must:
- Select the right SIEM solution (e.g., Splunk, QRadar, Azure Sentinel).
- Configure data collection from various sources.
- Develop and implement security use cases and alerts.
Configuring and Tuning Monitoring Tools
Monitoring tools need to be configured and tuned to optimize performance and reduce false positives. This involves:
- Fine-tuning alert thresholds.
- Customizing dashboards and reports.
- Regularly reviewing and updating configurations.
Analyzing and Responding to Security Events
This is the “action phase” of the security cycle.
Incident Detection and Analysis
Security Architects need to establish processes for:
- Alert triage: Prioritizing and investigating alerts.
- Analyzing the scope and impact of incidents.
- Identifying the root cause of security breaches.
Incident Response Planning and Execution
A well-defined incident response plan is critical. The architect should:
- Develop and document incident response procedures.
- Train security teams on incident response protocols.
- Conduct regular incident response exercises.
Threat Hunting and Proactive Defense
Going beyond reactive monitoring, threat hunting involves proactively searching for threats that may have bypassed existing security controls. This includes:
- Using threat intelligence to guide hunting activities.
- Developing custom detection rules.
- Analyzing historical data to uncover hidden threats.
Continuously Improving Security Processes and Tools
Security is not a “set it and forget it” proposition. It requires constant adaptation and improvement.
Automating Security Workflows
Automation is crucial for efficiency. Security Architects should explore:
- Automating alert triage and incident response tasks.
- Using SOAR (Security Orchestration, Automation, and Response) platforms.
- Automating vulnerability management and patching processes.
Vulnerability Management and Patching
Keeping systems up to date with the latest security patches is essential. The architect needs to:
- Implement a vulnerability scanning program.
- Prioritize patching based on risk.
- Establish a process for testing and deploying patches.
Staying Ahead of Emerging Threats
The threat landscape is constantly evolving. Security Architects must:
- Stay informed about new threats and vulnerabilities.
- Continuously assess the effectiveness of security controls.
- Adapt security strategies to address emerging risks.
Collaborating with Other Security Teams
Security is a team effort.
Fostering a Culture of Security Awareness
Educating employees about security best practices is essential. The architect can:
- Develop and deliver security awareness training.
- Conduct phishing simulations.
- Promote a culture of security consciousness.
Communicating Effectively: Reporting and Dashboards
Clear and concise communication is critical. Security Architects should:
- Develop regular security reports for stakeholders.
- Create dashboards to visualize security metrics.
- Communicate security incidents effectively.
Knowledge Sharing and Training
Sharing knowledge and training within the security team is crucial. The architect can:
- Encourage knowledge sharing among team members.
- Provide opportunities for professional development.
- Stay up to date on the latest security trends and technologies.
Technologies and Tools: The Security Architect’s Toolkit
Several technologies and tools are central to threat intelligence and monitoring.
- SIEM Solutions: Splunk, QRadar, Azure Sentinel, and others. These platforms collect, analyze, and correlate security data.
- Threat Intelligence Platforms (TIPs): Recorded Future, Anomali, and others. These platforms help manage and integrate threat intelligence feeds.
- Security Orchestration, Automation, and Response (SOAR): Swimlane, Demisto (now Palo Alto Networks Cortex XSOAR), and others. These platforms automate security tasks, such as incident response.
Measuring Success: Key Performance Indicators (KPIs)
Measuring the effectiveness of threat intelligence and monitoring efforts is vital. Key metrics include:
- Incident Response Time: The time it takes to detect, contain, and remediate security incidents.
- Threat Detection Rate: The percentage of threats successfully detected.
- False Positive Rate: The percentage of alerts that turn out to be non-malicious.
Future Trends in Threat Intelligence and Monitoring
The future of these areas will likely be shaped by:
- AI and Machine Learning: Leveraging these technologies for threat detection, analysis, and automation.
- Cloud-Based Security: Adapting to the shift towards cloud environments.
- Threat Intelligence Sharing: Increased collaboration and information sharing among organizations.
- Automation: Increasing the use of security orchestration and automation platforms.
Conclusion: Empowering the Security Architect
In conclusion, threat intelligence and monitoring are the cornerstones of a strong security posture. The Security Architect, acting as the conductor of this orchestra, orchestrates these functions, ensuring that organizations can anticipate, detect, and effectively respond to cyber threats. By mastering the principles and techniques outlined in this guide, Security Architects can build a robust defense that protects critical assets and empowers their organizations to thrive in today’s dynamic threat landscape. The evolution of cyber threats is constant, so the Security Architect must also be.
FAQs
What is the difference between threat intelligence and security monitoring?
Threat intelligence provides the knowledge about threats – who the attackers are, their motivations, and the techniques they use. Security monitoring is the practice of continuously observing and analyzing security-related data to detect anomalies and potential threats. While threat intelligence informs “what” the threats are, security monitoring answers the “how” and “when” of attacks.
How can a Security Architect integrate threat intelligence with security tools?
Threat intelligence can be integrated with various security tools such as SIEM, firewalls, and endpoint detection and response (EDR) systems. For example, integrating IOCs from threat intelligence feeds into a SIEM allows the system to automatically detect malicious activity in logs. Feeding threat intelligence into firewalls enables the blocking of known malicious traffic.
What are the key components of a robust security monitoring architecture?
A robust security monitoring architecture should include a comprehensive collection of data sources from all areas within a network, a scalable design, good performance without affecting other systems and applications, and a resilient structure that allows operations to continue if part of the architecture fails.
How can I improve my incident response time?
Improving incident response time involves a multi-faceted approach. First, streamline incident response procedures to ensure efficiency. Then, implement automation to speed up tasks. Regular training and exercises keep the team sharp, and constant monitoring and analysis allows the security team to stay prepared for future events.
How do I stay informed about the latest security threats?
Stay informed about emerging threats through various channels, including commercial threat intelligence feeds, open-source intelligence (OSINT) sources like blogs and forums, and information sharing and analysis centers (ISACs). Attend industry conferences, participate in online communities, and stay updated on the latest vulnerabilities and attack techniques.