table of contents
Vulnerability Management: Your Guide to the Security Analyst’s Role
Let’s get down to brass tacks! As a security analyst, navigating the world of vulnerability management is not just a task; it’s an adventure. Think of it as a constant battle against digital threats, a never-ending quest to fortify your organization’s defenses. We’ll break down what vulnerability management means, what the role of a security analyst entails, and the important tasks involved. We’ll also highlight the skills you need to excel and why this is a crucial area for any organization.
What is Vulnerability Management, Anyway?
Vulnerability management is the proactive process of identifying, assessing, prioritizing, and remediating security weaknesses (vulnerabilities) in your organization’s systems and applications. It’s like a comprehensive health checkup for your IT infrastructure. The goal is to find the chinks in your armor before malicious actors do. It involves a continuous cycle of scanning, analysis, action, and improvement to minimize the attack surface and reduce the potential impact of security breaches. Think of it as the foundation of any robust security posture. A well-executed vulnerability management program helps organizations safeguard sensitive data, maintain operational continuity, and comply with regulatory requirements.
It’s not a one-and-done deal; instead, it is an ongoing process that constantly adapts to the evolving threat landscape. The core components of vulnerability management are:
- Identification: Finding the vulnerabilities that exist.
- Assessment: Analyzing the risk associated with each vulnerability.
- Prioritization: Ranking vulnerabilities based on their severity and impact.
- Remediation: Taking action to fix or mitigate the vulnerabilities.
Diving into the Security Analyst’s Realm
So, where does the security analyst fit into this grand scheme? A security analyst is the quarterback of the vulnerability management team. They are the frontline defenders, responsible for executing the vulnerability management program. They conduct scans, analyze the results, communicate findings, and coordinate remediation efforts. Security analysts must be proficient with various security tools, understand IT systems, and have a knack for problem-solving. They are essential for keeping the organization safe from cyber threats.
They are the experts who are there to identify, assess, and remediate vulnerabilities. They play a critical role in ensuring the organization’s security posture. The security analyst’s daily tasks are diverse and challenging, but with the right skills and tools, they can make a real difference in protecting their organization.
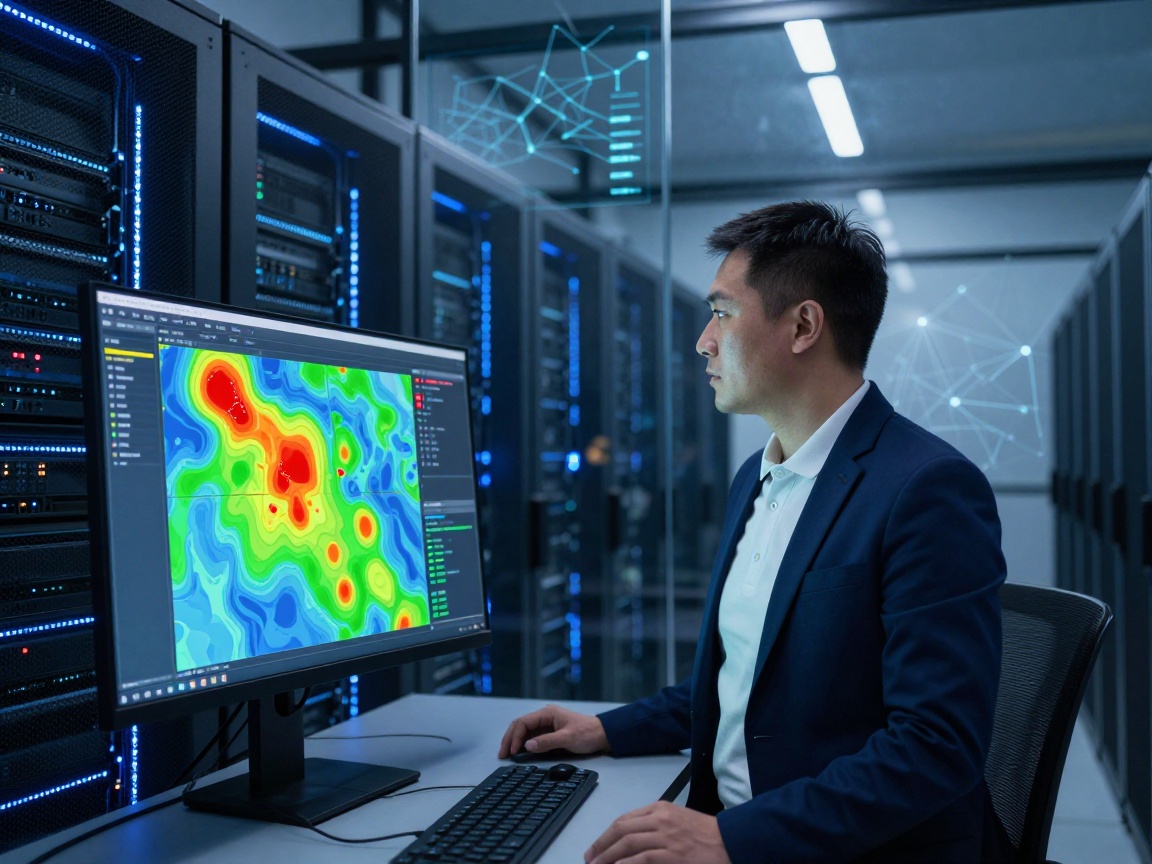
The Daily Grind: Vulnerability Scanning and Assessment
This is where the rubber meets the road. Vulnerability scanning and assessment are the bread and butter of the security analyst’s day. This involves using automated tools to scan systems, networks, and applications for known vulnerabilities. The analyst then reviews the scan results to understand the vulnerabilities discovered, their potential impact, and how to remediate them. It is an ongoing process that requires technical expertise, attention to detail, and the ability to interpret data.
The process usually includes:
- Network Scanning: Identifying devices on the network and their vulnerabilities.
- Web Application Scanning: Analyzing web applications for security flaws.
- Host-Based Scanning: Checking individual servers and workstations.
Unveiling the Secrets: Tools of the Trade
A security analyst would be lost without the right tools. These tools automate the scanning process and provide detailed reports about potential vulnerabilities. Some common tools include:
- Nessus: A well-regarded vulnerability scanner known for its extensive vulnerability database.
- OpenVAS: An open-source vulnerability scanner that provides a comprehensive assessment.
- Rapid7 InsightVM: A platform that automates vulnerability management.
- Qualys: A cloud-based security platform that offers vulnerability management and other security services.
Keeping Everyone in the Loop: Vulnerability Reporting and Communication
The security analyst is not just a tech whiz; they’re also a communicator. Once vulnerabilities are discovered, they need to be reported to the right people, from IT staff to management. This process involves creating reports that detail the vulnerabilities, their severity, the affected systems, and the recommended remediation steps. Effective communication is critical to ensure that everyone understands the risks and can take appropriate action.
Clear, concise reports are essential for getting buy-in and support for remediation efforts. The ability to translate technical jargon into understandable language is a must-have skill. A good security analyst can present complex information in a way that anyone can understand, from the IT team to upper management.
Speaking the Language of Risk: Prioritization
Not all vulnerabilities are created equal. Some pose a greater threat than others. Prioritization is the art of ranking vulnerabilities based on their potential impact and the likelihood of exploitation. Factors considered include:
- CVSS Score: Common Vulnerability Scoring System, a standardized metric.
- Exploit Availability: Are there public exploits available?
- Asset Value: How critical is the affected system?
Fixing What’s Broken: Vulnerability Remediation and Patching
This is the action phase, where vulnerabilities are addressed. Remediation involves fixing the vulnerabilities through patching, configuration changes, or other mitigation techniques. The security analyst often works closely with IT teams to ensure that remediation steps are implemented effectively and efficiently. The key is to get the right fix implemented as soon as possible.
Patching is a crucial aspect of remediation, but it can also be a challenge. Patching can sometimes cause unexpected issues or downtime, so it must be done carefully. Security analysts often need to test patches before deploying them widely and must have a rollback plan in case something goes wrong. They also need to ensure that patches are applied promptly to critical vulnerabilities, while other vulnerabilities are mitigated.
Patching: The Good, the Bad, and the Ugly
Patching is the most common remediation technique, but it is not without its challenges. It involves installing software updates to fix vulnerabilities. Patching is often seen as a necessary evil, requiring testing and careful planning. It can disrupt operations and introduce new issues.
Good patching involves:
- Timely Application: Applying patches as soon as possible.
- Testing: Testing patches before deployment.
- Documentation: Keeping a record of all patches applied.
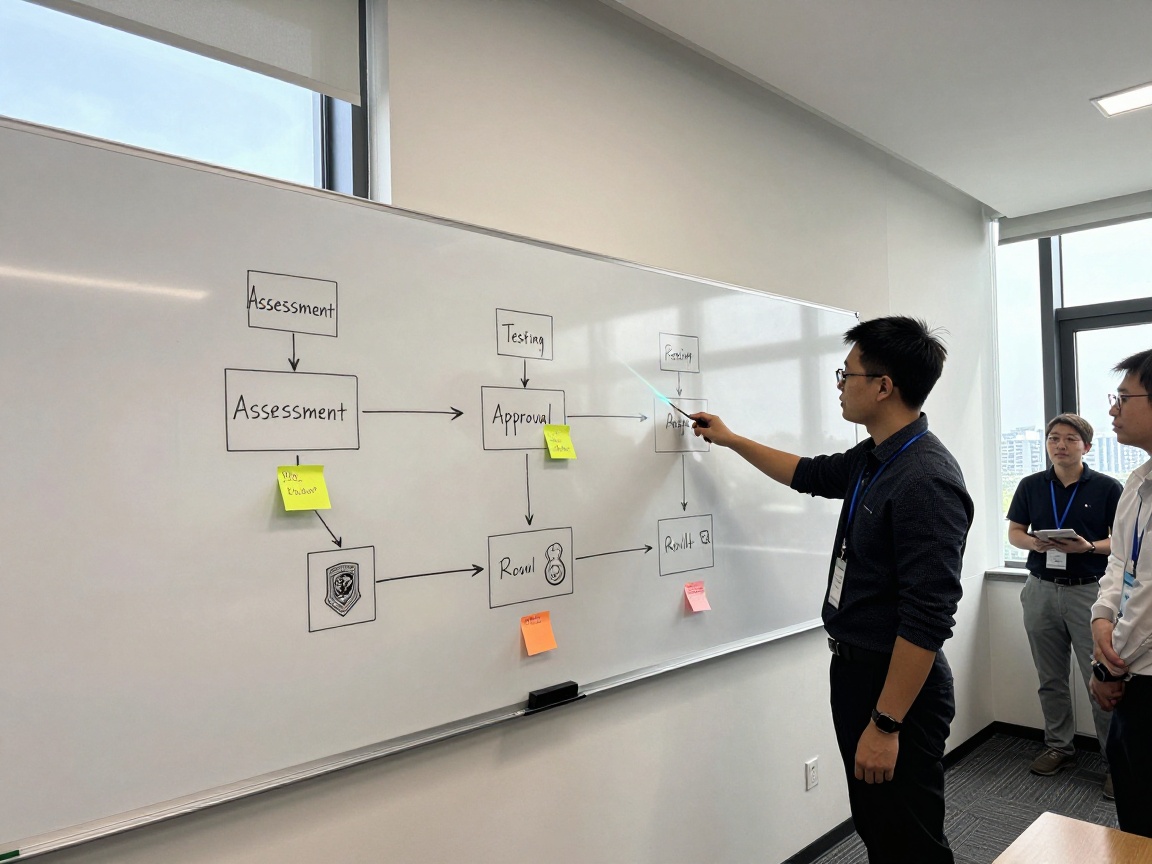
Building the Foundation: Vulnerability Management Policy and Process Development
A robust vulnerability management program needs a solid foundation. This means developing and implementing policies and processes that define how vulnerabilities are identified, assessed, remediated, and tracked. The security analyst often plays a key role in developing these policies and processes, which should align with industry best practices and regulatory requirements. This involves defining roles and responsibilities, establishing timelines, and documenting procedures.
Having a well-defined policy and process ensures consistency and effectiveness in your vulnerability management efforts. A well-defined policy covers all aspects of vulnerability management, including scanning frequency, remediation timelines, and communication protocols. These policies establish a framework for consistent and effective vulnerability management.
Seeing the Bigger Picture: Vulnerability Trend Analysis and Reporting
Vulnerability management is not just about fixing individual flaws; it is also about understanding the overall security posture of an organization. This involves analyzing trends in vulnerability data to identify patterns, assess the effectiveness of the vulnerability management program, and inform future security decisions. Trend analysis helps analysts to get the overall picture and track their organization’s security performance over time.
Reporting on vulnerability trends can help management understand the risks and make informed decisions about security investments. By identifying emerging threats and vulnerabilities, the security analyst can provide valuable insights that help organizations proactively protect themselves. This is about seeing the forest and the trees.
Data-Driven Decisions: Metrics that Matter
Data is king in trend analysis. Analysts track metrics to gauge the effectiveness of their programs, such as:
- Mean Time to Remediate (MTTR): How quickly vulnerabilities are fixed.
- Number of Open Vulnerabilities: The overall risk exposure.
- Vulnerability Density: The number of vulnerabilities per system.
Analyzing these metrics helps the security analyst understand the organization’s overall security posture and identify areas for improvement. They can use metrics to demonstrate the value of the vulnerability management program to stakeholders and secure resources for future improvements.
Automate, Automate, Automate: Vulnerability Management Tooling and Automation
Automation is the security analyst’s best friend. Automating tasks like scanning, reporting, and even remediation can save time, reduce errors, and improve efficiency. Automation can also help analysts respond quickly to emerging threats, which ensures that they’re better able to manage any risks. Using automation frees analysts up to focus on higher-level tasks, such as analyzing data and developing strategies.
Saving Time and Sanity: Examples of Automation
- Automated Scanning Schedules: Scheduling regular scans to identify vulnerabilities proactively.
- Automated Reporting: Generating reports automatically and distributing them to stakeholders.
- Patch Management: Automating the patching process to reduce manual effort.
Staying Sharp: Security Best Practices and Emerging Threats
The threat landscape is constantly evolving. To be effective, security analysts must stay informed about the latest security threats, best practices, and industry trends. They must continuously learn and adapt to the ever-changing landscape. This includes attending conferences, reading industry publications, and pursuing certifications.
Continuous Learning: The Analyst’s Secret Weapon
Security is a dynamic field, so continuous learning is a must. Staying up-to-date involves:
- Training Courses: Gaining certifications like CEH, CISSP, or CompTIA Security+.
- Industry Publications: Reading security blogs, journals, and newsletters.
- Conferences: Attending conferences to learn from experts and network with peers.
The Perks of a Pro: Why Vulnerability Management Matters
A well-executed vulnerability management program offers significant benefits to an organization. Here are some of the most important reasons why this is an essential discipline:
- Reduced Risk: Proactively identifying and fixing vulnerabilities reduces the likelihood of successful cyberattacks.
- Data Protection: Safeguards sensitive data from breaches and unauthorized access.
- Compliance: Helps meet regulatory requirements and industry standards.
- Improved Security Posture: Strengthens overall security defenses.
- Cost Savings: Prevents costly data breaches and downtime.
- Reputation: Maintains trust and confidence with customers and stakeholders.
Conclusion: Mastering the Vulnerability Landscape
Vulnerability management is not just a job; it’s a critical function. The security analyst is at the heart of this crucial process, working diligently to protect organizations from the ever-present threat of cyberattacks. By understanding the core concepts, mastering the tools, and staying up-to-date, security analysts can make a real difference in defending their organizations. Remember, in the world of cybersecurity, the work of a security analyst is never done, but that’s what makes it so rewarding.
FAQs
1. What are the most critical skills for a security analyst working in vulnerability management?
A security analyst needs a blend of technical skills and soft skills. They need a strong understanding of IT systems, networks, and security concepts. They should also be proficient with vulnerability scanning tools and have the ability to analyze scan results. Communication skills are vital for effectively reporting findings and collaborating with IT teams. Problem-solving and the ability to stay current with emerging threats are also essential.
2. How often should vulnerability scans be conducted?
The frequency of vulnerability scans depends on factors like the size and complexity of the network, the criticality of the systems, and the organization’s risk tolerance. It is important to define the frequency of scanning, which would vary depending on the system and business needs. Many organizations conduct regular scans, such as monthly, weekly, or even daily, along with scans after any significant changes to the environment. Critical systems might require more frequent scanning, while less sensitive systems can be scanned less often.
3. What is the difference between vulnerability scanning and penetration testing?
Vulnerability scanning is an automated process that identifies potential weaknesses in a system. It is a passive process, meaning it does not exploit any vulnerabilities. Penetration testing is a more in-depth, manual process that simulates a real-world attack to exploit vulnerabilities and assess the impact. Penetration testers use the information from the vulnerability scan to focus on the weaknesses. Penetration testing requires permission and is used to find how far an attacker can go.
4. What is the role of the security analyst in patch management?
The security analyst plays a key role in patch management, which involves identifying and applying software updates (patches) to fix vulnerabilities. The analyst researches and identifies relevant patches, assesses their potential impact, and works with IT teams to deploy the patches. Security analysts also often test patches, document all of the changes, and verify that the patches have been applied correctly and haven’t caused any issues. They are essential to making sure that your systems are up to date, safe, and secure.
5. How can I stay up-to-date on the latest vulnerabilities and threats?
Staying current with the latest threats is an ongoing process, requiring continuous learning and vigilance. You can stay up-to-date by subscribing to security blogs and newsletters, following security researchers and experts on social media, and regularly reviewing industry reports and advisories. The U.S. Cybersecurity & Infrastructure Security Agency (CISA) provides valuable resources, as does the National Vulnerability Database (NVD). Additionally, attending conferences, pursuing certifications, and participating in training programs will help you stay informed.